Improving your IT security goes beyond just safeguarding your personal and professional information – it also helps to prevent costly downtime, maintains your company’s reputation, and ensures regulatory compliance. Given the increasing incidents of hacking and information leaks, securing one’s digital resources has become more essential than ever.
This post will provide an overview of a few quick steps you can take to strengthen your cyber defenses. From updating all software and operating systems to establishing strong password practices and implementing firewalls for your network, we’ll show you how to safeguard your network. We’ll also discuss the importance of limiting access to certain networks and devices and backing up critical data regularly.
Step 1: Update All Software and Operating Systems
Updating your software and operating systems may seem like a small task, but it can make a big difference in protecting your computer from cyber threats. Entities with outdated software and operating systems are easy targets for cybercriminals.
Old systems lack the necessary patches and updates that address security vulnerabilities, making them a prime target for cyber attacks. Cyber attackers can easily steal your sensitive data, install malware or gain control over your system if you don’t patch your vulnerabilities.
It not only protects you from data security attacks but also enhances the overall performance of the system. When you update your software, you get access to the latest features and patches that address any security issues that may exist.
Regular updates ensure that you have the most up-to-date software and operating systems that are compatible with the latest hardware and software configurations. It also provides peace of mind knowing that your data is secure and your system is functioning at optimal levels.
Step 2: Establish Strong Password Practices
By setting strong passwords, you are creating a barrier between your sensitive information and malicious actors.
When creating passwords, it’s important to choose ones that are difficult for others to guess. Use a unique combination of upper and lower case letters, symbols, and numbers for a strong password. Also, avoid using personal information such as your name, date of birth, or address as they are easy to find online. Instead, use unique character combinations known only to you to secure your accounts.
Another way to create secure passwords is by using password managers. Let password generators do the work for you – generate and remember complex passwords – so you don’t have to.
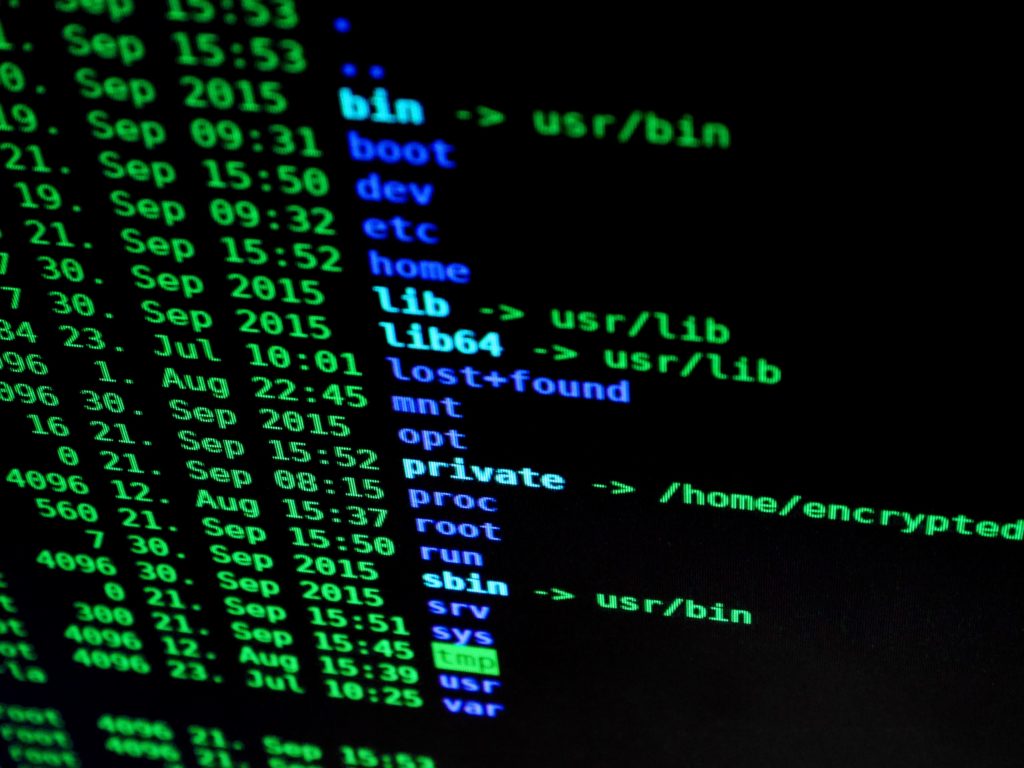
Encrypting Sensitive Data with Passwords
In addition to choosing secure passwords, it’s important to encrypt sensitive data with passwords. Encryption is a process of converting information into a secret code, which can only be accessed by authorized users who have the decryption key.
Pick a reliable encryption tool and store your decryption key safely to keep your data secure. For example, you can use file compression software that has built-in encryption capabilities, or you can use online storage services that offer encryption. It’s important to make sure that you choose a reliable tool and that you keep your decryption key in a safe place.
By following these two simple practices, you can significantly improve your IT security and protect your sensitive information from unauthorized access.
Step 3: Implement Firewalls for Your Network
Implementing firewalls for your network is an essential step in improving your IT security. By choosing the right type of firewall and configuring it correctly, you can protect your network against cyber attacks and ensure the safety of your data.
Follow the best practices outlined in this section to ensure that your firewall is functioning correctly and effectively protecting your network.
Types of Firewalls and How They Work
There are several types of firewalls available in the market, but the most commonly used types are hardware firewalls, software firewalls, and cloud firewalls.
- Hardware Firewalls: You install hardware firewalls as physical devices between your network and the internet to enhance security. They examine incoming traffic, compare it to a set of predefined rules, and block any traffic that does not meet those rules. Hardware firewalls are effective in protecting your network against external threats and are usually used in larger organizations.
- Software Firewalls: These are programs that run on your computer or server and examine incoming traffic. They are usually used in smaller organizations or for personal use. Software firewalls are effective in blocking incoming traffic from specific IP addresses or blocking certain types of traffic, such as email spam.
- Cloud Firewalls: These are firewalls that are managed by a cloud provider and are usually used in cloud-based environments. They operate in a similar way to hardware and software firewalls but are managed by the provider, making them easier to maintain and manage.
Best Practices for Configuring Firewalls
Once you have chosen the type of firewall that suits your organization, it’s time to configure it correctly to ensure maximum security. Here are some best practices for configuring firewalls:
Create a Firewall Policy: A firewall policy is a set of rules that dictate how traffic should be handled by the firewall. It’s essential to create a firewall policy that aligns with your organization’s security requirements. A well-defined firewall policy can help you block malicious traffic and ensure that legitimate traffic can pass through the firewall without any issues.
Update Your Firewall Regularly: Firewalls need to be updated regularly to ensure that they can protect against the latest threats. Make sure to update your firewall firmware, operating system, and security software regularly.
Test Your Firewall: It’s essential to test your firewall regularly to ensure that it’s functioning correctly. Regular testing can help you identify vulnerabilities and security gaps that need to be addressed.
Step 4: Limit Access to Certain Networks and Devices
Controlling who has access to your network and resources is critical to maintaining security. It’s essential to limit access to sensitive data and systems to only those who need it.
Here are some best practices for controlling access:
Create User Accounts: Create user accounts for each employee or user, and assign permissions to access specific resources. This allows you to control who has access to which data and systems.
Limit Administrative Access: Limit administrative access to only those who need it. This reduces the risk of unauthorized access and prevents employees from making changes to critical systems accidentally.
Implement Role-Based Access Control: Role-based access control (RBAC) is a method of granting access based on the user’s role or job function. It helps you control access to resources and reduces the risk of unauthorized access.
Using Multi-Factor Authentication for Added Protection
Multi-factor authentication (MFA) is an additional layer of security that requires users to provide multiple forms of identification to access resources or systems. This can include a password, a fingerprint, or a security token. Here are some benefits of using MFA:
Increased Security: MFA provides an additional layer of security to protect against unauthorized access. It’s much harder for hackers to gain access to your systems if they need multiple forms of identification.
Reduced Risk of Data Breaches: MFA reduces the risk of data breaches by making it harder for hackers to gain access to your systems. Even if a password is compromised, MFA can prevent unauthorized access.
Improved Compliance: Many regulatory frameworks require the use of MFA to protect sensitive data. Implementing MFA can help you comply with these regulations and avoid penalties.
Step 5: Back Up Critical Data Regularly
Backing up critical data regularly ensures the security and reliability of your IT systems.
There are several methods of backing up data, including:
External Hard Drives: External hard drives are a popular and affordable option for backing up data. They are easy to use and provide a physical backup of your data that can be stored offsite for added security.
Network Attached Storage: Network attached storage (NAS) is a centralized storage system that allows multiple users to store and access data from a single location. It provides a secure and reliable backup solution for organizations with multiple users.
Tape Backup: Tape backup is a legacy backup method that involves writing data onto magnetic tape. While it is slower than other methods, it is still used in some industries because it provides an affordable and reliable backup solution.
Cloud Storage and Backup: Cloud storage solutions provide several advantages over traditional backup methods. Here are some of the benefits of using cloud storage for data backup:
- Scalability: Cloud storage solutions can easily scale up or down based on your organization’s needs. You can increase storage capacity as your data grows, without needing to purchase additional hardware.
- Accessibility: Cloud storage solutions provide easy access to your data from anywhere with an internet connection. This makes it easy for employees to access critical data when they are working remotely or traveling.
- Security: Cloud storage providers have robust security measures in place to protect your data against cyber threats. This includes data encryption, multi-factor authentication, and regular backups to multiple data centers.
Take a Few Minutes and Improve your IT Security
IT security is an essential aspect of modern-day technology usage, and staying ahead of potential cybersecurity threats is critical. The 15-minute steps outlined in this blog post provide practical and easy-to-implement measures that can help anyone improve their IT security.
By updating software and operating systems, establishing strong password practices, implementing firewalls, limiting access to certain networks and devices, and backing up critical data regularly, individuals and businesses can significantly reduce the risk of cyber attacks.
It’s essential to note that cyber threats are continuously evolving, and staying vigilant and proactive is necessary to maintain adequate protection. By implementing these measures, individuals can take significant steps towards securing their online presence and safeguarding their sensitive information from potential cyber threats. To learn more about how Silver Tree can improve and enhance your IT security posture, contact us here.


